Protect Data on your Computer: People use computers every day. You turn on your PC not only to work but also to relax. However, few users think about protection. As a result, they are attacking hackers. It can happen when they use unprotected platforms and when they open trustworthy platforms such as the best live casino sites. These tips will help you stay safe and prevent your data from being lost.
Table of Contents
Protect Data on your Computer – Keep Programs And Apps Up To Date
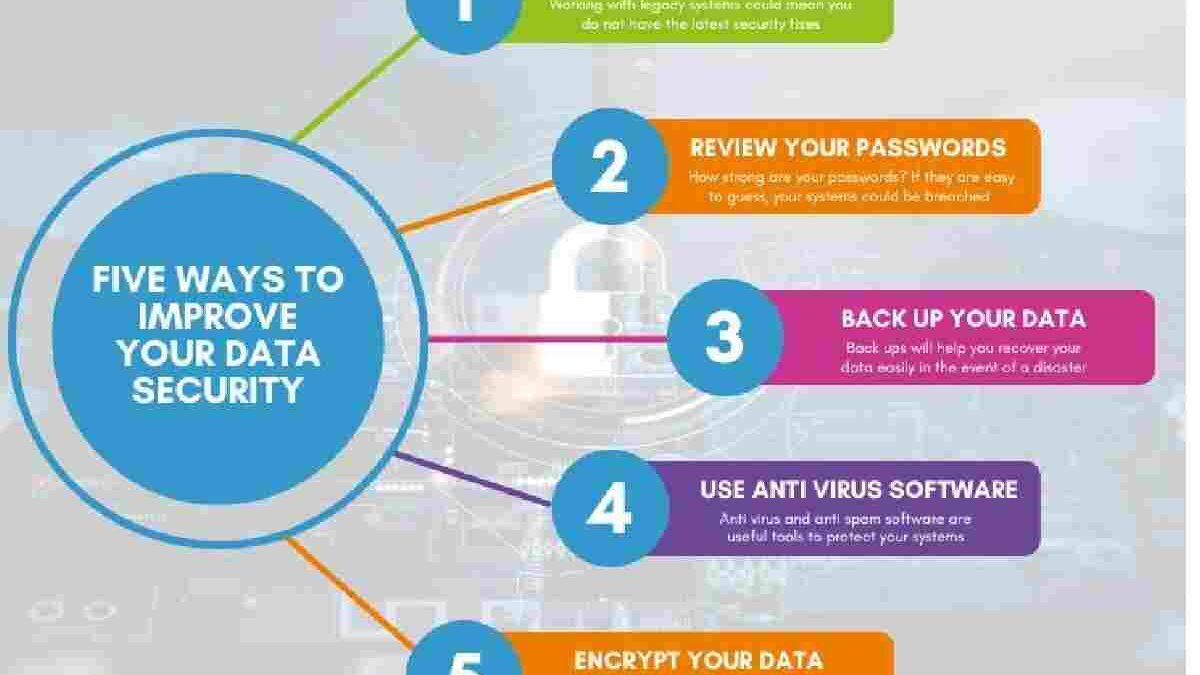
Many hackers exploit vulnerabilities in outdated programs. So check the version of your browser, PDF reader, and other utilities. You will be less likely to fall victim to attackers with a current version, as manufacturers patch their products after new viruses appear. Deferring updates is like leaving your apartment door unlocked.
Ratings do not only apply to individual programs. Remember to update router and modem firmware and install operating system updates. And you don’t need to have the latest operating system. For example, Windows 7 is sufficient. In most cases, security updates will even release to older operating system versions. However, this does not apply to Windows XP. Stop using it to protect yourself because this version is too outdated.
Protect Data on your Computer – Use A Password Manager
Many people use two or three passwords for all of their accounts. Still, it’s very dangerous. It’s not that scary if your account with a music service is hacking. However, if you use the same password in an online bank, you could lose your savings.
So that you don’t have to memorize dozens of combinations, install a unique program that will automatically create complex combinations and save them for you. It’s a password manager. According to the researchers, people generally use too easy-to-remember and straightforward combinations. So let a password manager create your passwords.
It is more convenient and secure to use a passphrase. So it suffices to find a single combination. But it must be very strong. Forget about capitals, symbols, and numbers. A few words are not related in meaning but are easy to pronounce and remember.
It may seem dangerous to store passwords in a third-party manager. However, it is unlikely that a hacker will deliberately attack your password database. On the other hand, there is a strong possibility that attackers could obtain the code you are using for multiple services by compromising one of them.
Do not use Flash Player
It is probably one of the most vulnerable programs on your computer. Fortunately, most of the services are no longer using it, so feel free to uninstall it. Or at least change your browser settings so that Flash doesn’t run automatically.
Don’t install Questionable Extensions
Depending on their function, extensions can access a large amount of your data, such as your browsing history. So choose your programs very carefully. Install what you need and only from the official Or even change the way data is presented to you.
Use a VPN
When you connect to a Wi-Fi network in a public place (coffee shop, airport, or hotel), you share the network with strangers. And if an intruder is on them, they can intercept your data. While the connection is now more secure thanks to the proliferation of HTTPS, a VPN service like Surfshark can help. With this program, you first connect to a virtual private network and then to the entire Internet. It gives you an extra layer of protection.
Remember, this is not a panacea. Choose the right service and don’t forget to use it. A VPN masks your IP address but does not protect you from downloading a malicious file or entering a phishing site.
Make Copies Of Important Files
If you are concerned that intruders will destroy or block essential documents, it is very important to create duplicates. Take it offline and save copies on an external hard drive that is not connecting to your computer.
Don’t Give Too Much Information About Yourself
Don’t post credit card or boarding pass photos on social media. In general, try to talk about your life as little as possible. Remember that social media posts are available to all internet users. There is a risk even if you have a closed
profile. People you already know, or people you stopped communicating with but haven’t removed from your followers, are perfectly fine to take a screenshot and share the information with someone else.
Also, think about the data that you share without even knowing it. For example, your approximate address can be guessed from your running routes in a running app or geotags on Twitter. Further data to determine on the basis of this information. The more data an attacker has, the more he tries to access your accounts.